Next-Generation Network Detection & Response
Autonomous Cyber Defense Platform redefining network security.

Network Detection & Response
Advanced NDR with real-time, ML-powered threat detection
- Real-time network traffic analysis
- Behavioral anomaly detection
- Encrypted traffic inspection
- Automated threat response
Extended Detection & Response
Unified visibility and response across your entire security stack
- Cross-platform correlation
- Automated investigation
- Orchestrated response
- Threat hunting tools
Enterprise Log Manager
Transform massive log data into actionable security intelligence
- Universal log collection
- Real-time correlation
- Compliance automation
- Advanced analytics
Built for Modern Security Challenges
Extensible architecture that adapts to your needs
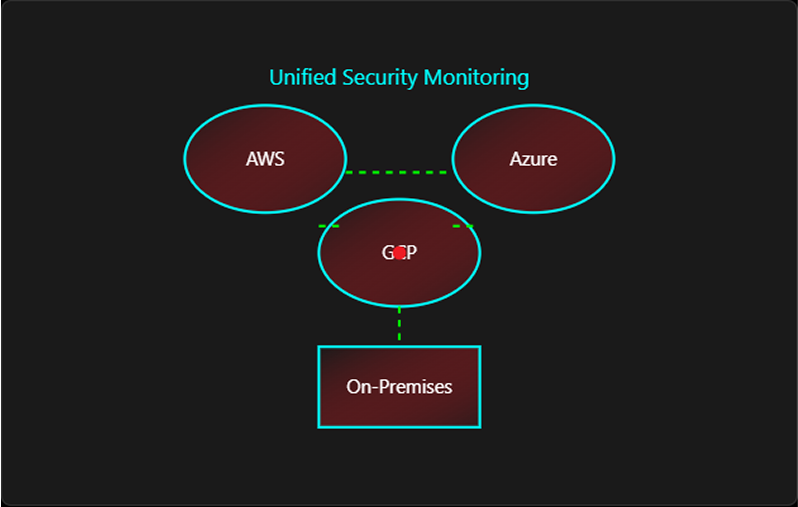
Your Infrastructure, Your Choice
Deploy 100% on-premises for complete data sovereignty, 100% cloud for unlimited scalability, or hybrid for the best of both worlds. No compromise on features or performance.
- On-premises deployment for data control
- Cloud deployment for infinite scale
- Hybrid options for flexibility
- Support for air-gapped deployment in critical environments
Complete Visibility, Zero Overhead
Achieve comprehensive network visibility without installing agents. Our passive monitoring approach ensures no performance impact on endpoints or network infrastructure.
- 100% passive monitoring
- No endpoint agents required
- Zero performance degradation
- Complete traffic visibility across IT & OT
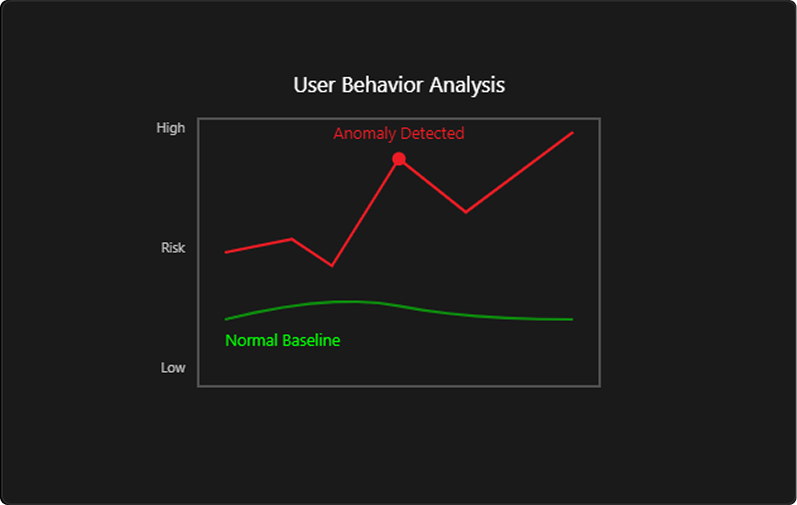
Stay Ahead of Zero-Day Threats
Advanced machine learning algorithms detect unknown threats and anomalous behaviors in realtime. Continuously learning and adapting to your network's unique patterns.
- ML-powered anomaly detection
- Behavioral baseline learning
- Zero-day threat identification
- Continuous model updates
From Detection to Prevention in Seconds
Orchestrate responses across your entire security stack. Reduce MTTR from hours to minutes with automated containment and remediation workflows.
- Automated response orchestration
- Cross-platform integration
- One-click response
- Customizable playbooks
Solving Real Security Challenges
See how AttackFence addresses your critical security needs
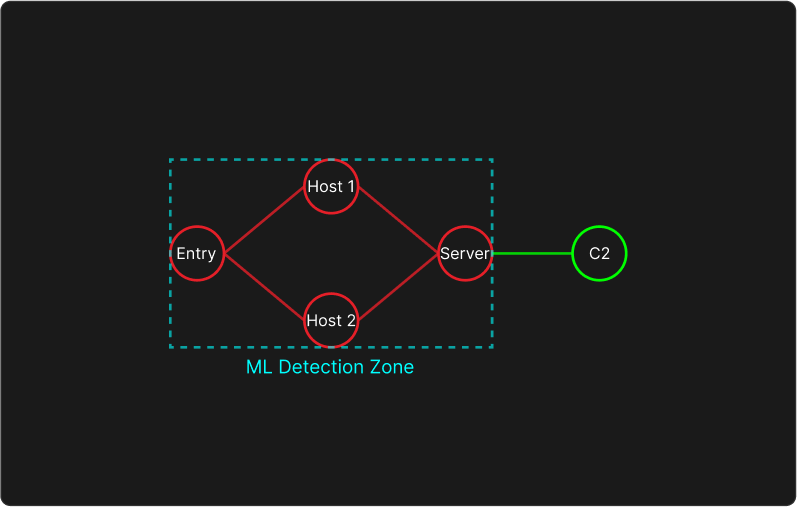
Advanced Persistent Threat Detection
Problem
Sophisticated attackers use stealthy techniques to maintain long-term network access, evading traditional security measures
Solution
Our ML-powered NDR identifies subtle anomalies and attack patterns, detecting APTs that signature-based tools miss
- Continuous behavioral monitoring across all network traffic
- Detection of lateral movement and data staging
- Identification of command & control communications
- Automated threat timeline reconstruction
Outcome: Reduce threat dwell time from months to hours with continuous behavioral monitoring
Insider Threat Detection
Problem
Malicious or negligent insiders pose significant risks, with privileged access making detection challenging
Solution
Monitor user behavior patterns, detect anomalous data access, and track lateral movement across your network
- Multi-pronged behavior analytics engine
- Abnormal data access pattern detection
- Unauthorized access monitoring
- Data exfiltration prevention
Outcome: Identify suspicious insider activities before data breach occurs
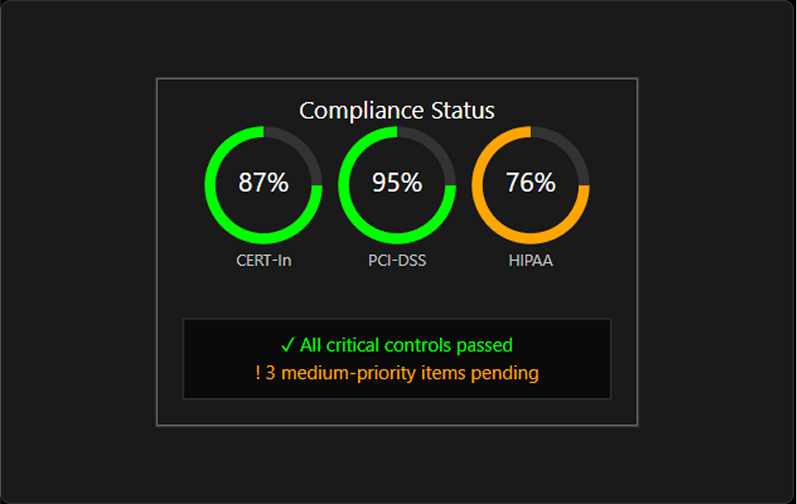
Compliance Monitoring
Problem
Meeting regulatory requirements demands continuous monitoring, reporting, and audit trail maintenance
Solution
Automated compliance reporting with pre-built templates for CERT-In, and custom frameworks
- Pre-configured compliance templates
- Automated evidence collection
- Real-time compliance dashboards
- Scheduled report generation
Outcome: Transform compliance from a burden to an automated process
Cloud Security Monitoring
Problem
Limited visibility into cloud workloads creates security blind spots in hybrid environments
Solution
Extend NDR capabilities seamlessly across cloud platforms with multiple operating modes: full packet inspection and flow ingestion
- Multi-cloud platform support
- Cloud behaviour analytics
- Cloud-native threat detection
- Hybrid environment correlation
Outcome: Unified security posture across on-premises and cloud infrastructure
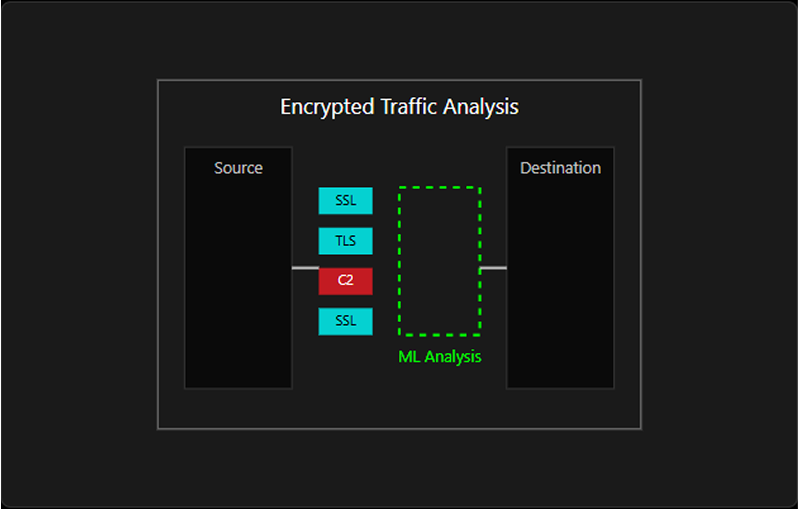
Network Traffic Analysis
Problem
Encrypted traffic hides threats, while decryption compromises privacy and performance
Solution
Entropy-based anomaly detection analyzes encrypted traffic patterns without decryption
- SSL/TLS traffic analysis without decryption
- Application fingerprinting
- Certificate anomaly detection
- Beaconing pattern identification
Outcome: Detect threats in SSL/TLS traffic while maintaining privacy and compliance
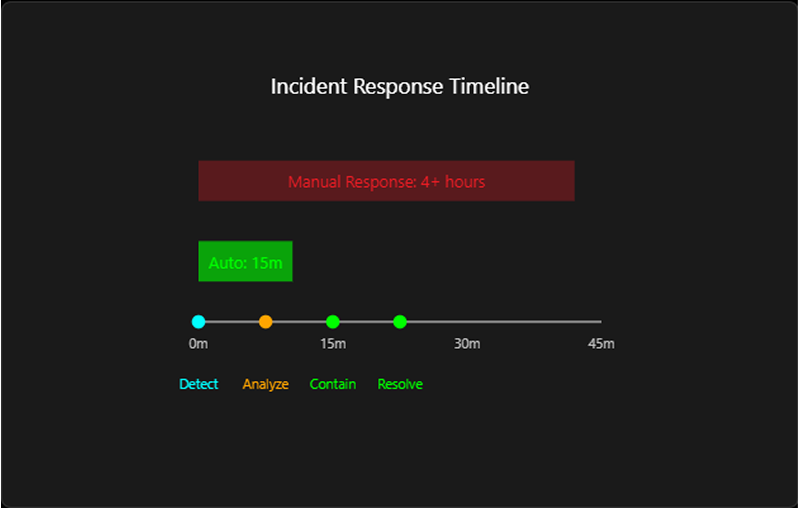
Incident Response Acceleration
Problem
Manual incident response processes lead to extended breach impact and higher costs
Solution
Automated alert correlation, threat context enrichment, and orchestrated response actions
- Co-ordinated playbook execution
- Cross-platform response orchestration
- Evidence collection and preservation
- Advanced threat hunting capabilities
Outcome: Minimize breach impact with rapid, coordinated response
Supercharge Your Security Operations Center
Transform your SOC from reactive to proactive with intelligent insights
SOC Transformation Dashboard
Before AttackFence
10,000+
Daily alerts overwhelming analysts
After AttackFence
50-100
Prioritized, actionable alertsUnified Visibility
Before: 15+ security tools, multiple dashboards
After: Single pane of glass view for all security data
Reduce Alert Deluge
Before: 10,000+ daily alerts, 80% false positives
After: 50-100 Prioritized, actionable alerts
Accelerate Investigation
Before: Hours spent correlating data across tools
After: Automated correlation with full context
Automate Response
Before: Manual response taking 4+ hours
After: Automated containment in minutes
Security Resources & Insights
Deepen your knowledge with our expert insights

AttackFence Log Manager
AttackFence® Log Manager ingests, categorizes, and stores massive log volumes efficiently, supporting up to 500,000 events per second.

AttackFence XDR
AttackFence® XDR delivers context-rich detection, visibility, and automated response by integrating telemetry from endpoints, applications, and networks seamlessly.

AttackFence NDR
AttackFence® NDR empowers enterprises with advanced threat detection, real-time response, and unparalleled visibility across dynamic network environments.

AttackFence NBAD
AttackFence® NBAD leverages advanced behavior analysis to detect anomalies and redefine enterprise network security in evolving digital landscapes.
Ready to Transform Your Security?
Let's discuss how AttackFence can protect your organization
Get in Touch
Phone
Address
AttackFence Techlabs Pvt. Ltd.
426,428, Tower A, Spaze i-Tech Park
Sector 49, Sohna Road
Gurugram-122018






